
Why You Should Spend More Time Thinking About WHAT IF?
/Why You Should Spend More Time Thinking About WHAT IF? Are you a cautious person? Do you like to have a back-up plan? Do you keep a torch or candles somewhere easy to reach in case of a power cut? Do you carry a map in case your sat-nav dies? How about a pocket charger […]
Read more
Insurtech – Build Connectivity with Customers and Boost Your Bottom Line
/Insurtech – Build Connectivity with Customers and Boost Your Bottom Line Insurtech – Sounds like it’s short for Insurance and Technology… well, that’s exactly what it is. So that’s the word sorted out… what does it do and, more importantly, “what can it do for your business?” Insurtech is any new technology introduced into an […]
Read more
Intel’s memory leaking Processor – The embargo is lifted, and the threat is real
/Intel’s memory leaking Processor – The embargo is lifted, and the threat is real Frame rates, Security issues for Linux, OS X and Windows users caused by structuring oversight by not just Intel chips, but Arm and AMD processors – to varying degrees. An issue has been found in Intel’s processor chips that has forced […]
Read more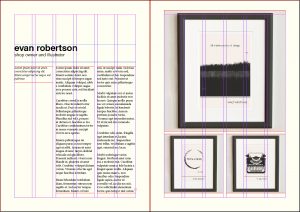
GRIDS – LAYOUT ESSENTIALS
/“Grids are the most misunderstood and misused element in page layout. A grid is only useful if it is derived from the material it is intended to handle.” – Derek Birdsall Notes on book Design GRIDS AND HOW TO USE THEM! Establishing a solid grid structure forms the backbone of web media, page, email, everything. […]
Read more
Kaspersky Data Theft Watershed
/ | Leave a CommentKaspersky Data Theft Watershed Over the past month, numerous articles detailing the possible collusion with Kaspersky have come to the surface. At the start of October, it was revealed by the BBC that Israeli spies ‘watched Russian agents breach Kaspersky software’ (https://www.bbc.co.uk/news/technology-41580850). This discovery was made of course after they had also breached the software. […]
Read more
Single source of customer Intelligence
/ | Leave a CommentSingle source of customer Intelligence The executives’ challenge is creating a single view of customer engagement. When companies fail to meet customer expectations – which happens all too often – insufficient access to customer data is usually to blame. Only 13 percent of 680 executives who responded to a recent Harvard Business Review Analytic Services […]
Read more
Mitigating threats posed by Terminated Employees
/ | Leave a CommentMitigating threats posed by Terminated Employees Experts say the risks are too often overlooked Federal regulators are reminding healthcare entities and business associates of the serious security and privacy risks that terminated employees can pose and offering advice for mitigating those risks. Data breaches caused by current and former workforce members are a recurring issue, […]
Read more